Yesterday, the 5th Annual GROW Pasco event unfolded at the Saint Leo University Wellness Center, bringing together entrepreneurs, business leaders, and innovators from across Pasco County. Hosted by SMARTstart, the event aimed to educate and connect business owners, fostering a community of growth and collaboration.
A day filled with 15 insightful breakout sessions led by over 30 business professionals covered diverse topics, including digital trends, artificial intelligence, marketing strategies, and local business resources. These sessions provided attendees with valuable insights and strategies to navigate the evolving business landscape.
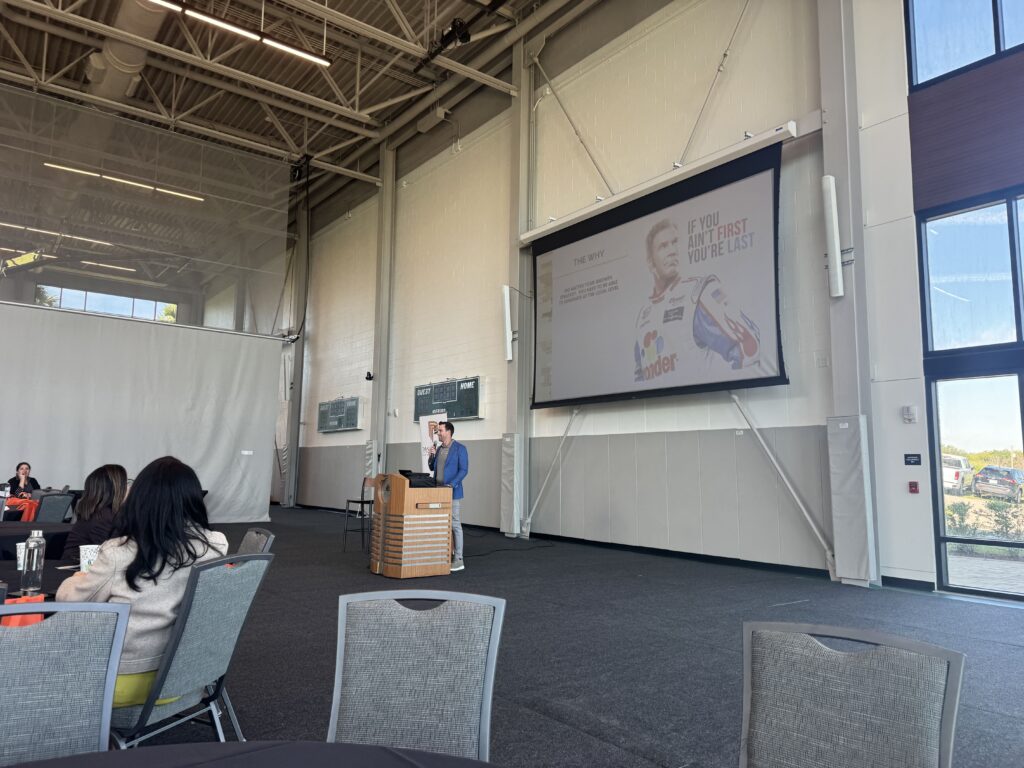
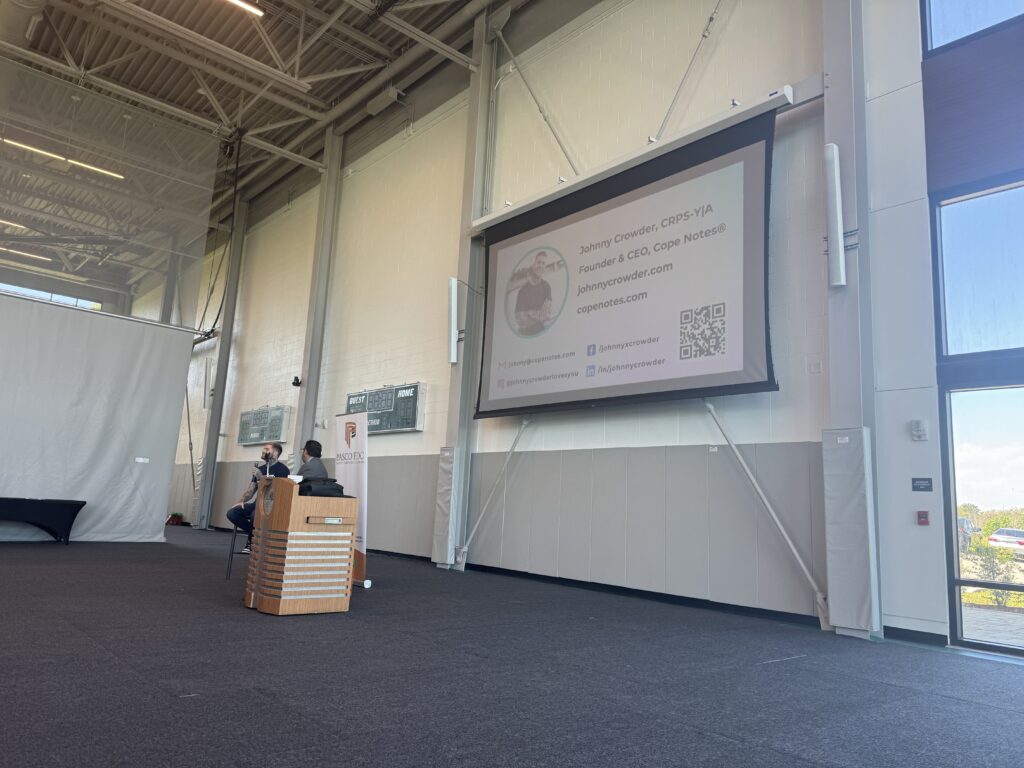
A highlight of the day was the keynote presentation by Johnny Crowder, founder and CEO of Cope Notes. As a suicide and abuse survivor, TEDx speaker, and certified peer recovery specialist, Johnny shared their journey and emphasized the importance of mental health and wellness in the business community.
Participating as a panel speaker, I had the privilege of discussing technological impacts on small businesses. I am incredibly grateful to my fellow panel members and all the speakers throughout the day for their invaluable contributions. Your expertise and dedication have made a significant impact in driving our community forward.
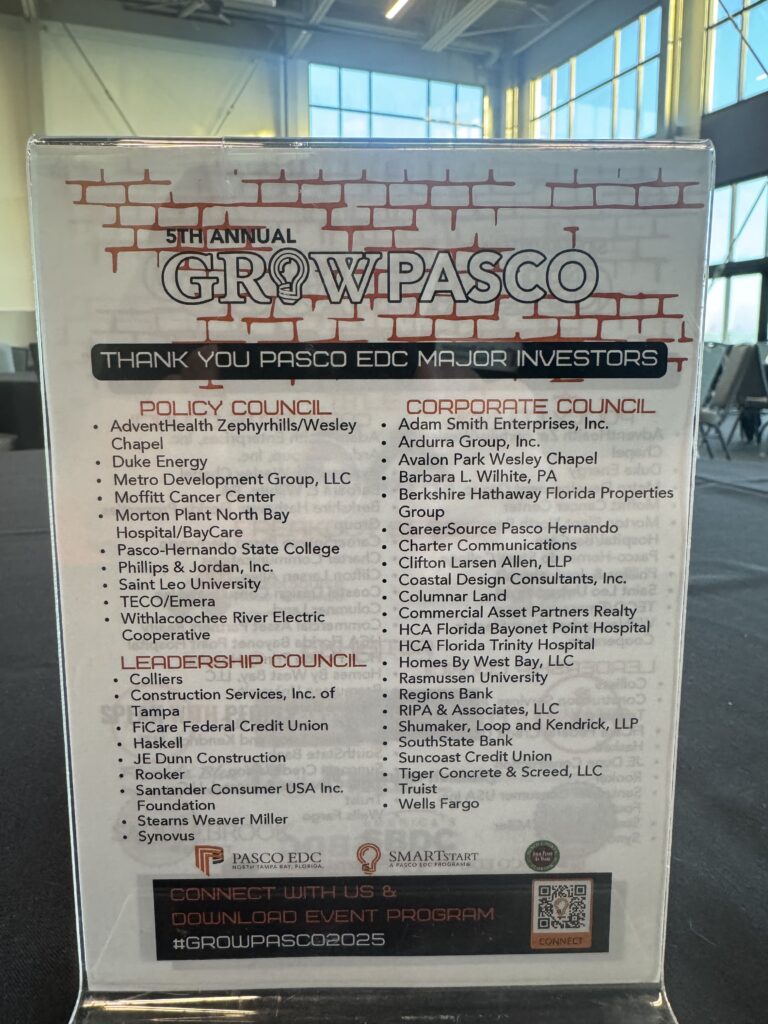
We are thrilled to announce that events like GROW Pasco 2025 are made possible through the generous support of our sponsors. We are deeply grateful to our title sponsor, E-Assessment, Inc., and our breakout session sponsors, including the Pasco County Board of County Commissioners and Saint Leo University. Your commitment to fostering entrepreneurship and growth in our community is truly appreciated.
We warmly invite all attendees and community members to share their experiences and photos from today’s event. Use the hashtags #GROWPasco2025, #EmpowerPasco, and #PascoStrong to connect with others and keep the conversation going. We encourage you to continue sharing your experiences and ideas, contributing to the vibrant business community we are building together.
For those inspired to take an active role in our business community, consider engaging with the Pasco Economic Development Council (Pasco EDC) and SMARTstart programs. These initiatives offer resources, networking opportunities, and support to help you grow your business and contribute to our vibrant community.
As we reflect on the insights gained and connections made today, let’s continue to support each other in our entrepreneurial journeys. Together, we can build a thriving business ecosystem in Pasco County. Join us in shaping the future of Pasco County. Stay tuned for upcoming events and opportunities to get involved. Together, we are #PascoStrong.